Home>Home Security and Surveillance>When Should I Not Have An Intrusion Detection System


Home Security and Surveillance
When Should I Not Have An Intrusion Detection System
Modified: March 21, 2024
Learn about when it might not be necessary to have an Intrusion Detection System for your Home Security and Surveillance. Find out the factors to consider.
(Many of the links in this article redirect to a specific reviewed product. Your purchase of these products through affiliate links helps to generate commission for Storables.com, at no extra cost. Learn more)
Introduction
When it comes to home security and surveillance, an Intrusion Detection System (IDS) is often seen as a crucial component. It helps protect your property, belongings, and loved ones by detecting and alerting you to potential intrusions or security breaches.
However, it is essential to understand that not every situation or environment requires an IDS. There may be instances where investing in and implementing an IDS may not be the most practical or effective solution. In this article, we will explore several scenarios in which having an IDS may not be necessary or appropriate.
Before we dive into the specific situations, it is important to note that the decision to have or not have an IDS should be based on a comprehensive assessment of your unique circumstances. This article aims to provide you with insights and considerations to help you make an informed judgment.
Key Takeaways:
- Not every home needs an Intrusion Detection System (IDS). Factors like limited resources, low-risk environments, and expertise limitations should be considered. Alternative security measures can still enhance home security effectively.
- Legal constraints, cost-effectiveness, and industry-specific requirements play a crucial role in deciding whether to invest in an IDS. Understanding your unique situation and assessing these factors is key to making an informed decision.
Read more: When Was Intrusion Detection Introduced
Lack of Sufficient Resources
One of the primary factors to consider when deciding whether to invest in an IDS is your available resources. Implementing and maintaining an IDS requires a significant financial commitment as well as ongoing time and effort.
If you find yourself with limited financial resources, it may be challenging to allocate funds toward purchasing the necessary hardware and software for an IDS. Additionally, IDS systems often require regular updates and maintenance to ensure optimal functionality, which can further strain your resources.
Furthermore, IDS systems require expertise and knowledge to set up and configure properly. If you lack the necessary technical skills or cannot afford to hire an expert to install and maintain the system, it may not be practical to invest in an IDS.
In such cases, it may be more effective to focus on other security measures that are within your means, such as reinforced doors and windows, security cameras, and strong perimeter fencing. While these measures may not provide the same level of intrusion detection as an IDS, they can still significantly enhance your home security.
Ultimately, it is essential to assess your available resources and prioritize how best to allocate them to ensure the overall security of your home or property.
Low Risk Environment
Another situation in which you may not need an Intrusion Detection System (IDS) is if you live in a low-risk environment. Certain neighborhoods or locations may have lower crime rates or minimal history of security breaches, making the implementation of an IDS unnecessary.
If you reside in an area where theft, vandalism, or other security threats are rare, your resources might be better invested in other preventive measures or security improvements specific to your property.
For instance, you can focus on installing robust locks, security cameras, and adequate lighting to deter potential intruders. By strengthening the physical security of your home, you can greatly reduce the likelihood of a break-in or security breach.
However, it is important to note that even in seemingly safe environments, unexpected incidents can still occur. It is advisable to conduct a thorough risk assessment and consider factors such as the value of your assets, personal safety concerns, and the potential impact of a security breach on your overall well-being.
In some cases, even if the risk of external threats is low, you may still want to have some level of surveillance and security monitoring for peace of mind. This could involve installing simple home alarm systems or implementing remote monitoring solutions that allow you to keep an eye on your property when you are away.
Ultimately, the decision to forgo an IDS in a low-risk environment should be based on a realistic assessment of the actual security risks and your personal comfort level in relation to potential threats.
Industry-Specific Exceptions
In certain industries or sectors, there may be specific regulations or guidelines that require the implementation of an Intrusion Detection System (IDS). These regulations are often put in place to safeguard sensitive data, protect intellectual property, or ensure the security of critical infrastructure.
For example, organizations operating in sectors such as finance, healthcare, or government may have legal and compliance obligations to maintain a robust security infrastructure that includes an IDS. These industries handle valuable and sensitive information, making them prime targets for cyberattacks or physical breaches.
If your business operates in such an industry or deals with information that requires a higher level of security, it is crucial to carefully assess and comply with the regulatory requirements specific to your sector. Failure to do so can result in severe penalties or reputational damage.
Even if you are not mandated by regulations, it is important to consider the potential risk and impact of a security breach within your industry. Investing in an IDS can provide an added layer of protection, help detect and respond to security incidents promptly, and demonstrate a commitment to safeguarding sensitive information.
However, for individuals or small businesses operating outside of these regulated industries, it may be more practical to focus on other security measures that align with their specific needs and risk profile.
Ultimately, determining whether an IDS is necessary in your industry should be guided by industry-specific requirements, risk assessments, and the overall security objectives of your business.
Non-Internet Facing Systems
Another scenario where an Intrusion Detection System (IDS) may not be needed is when you have non-internet facing systems. In some cases, your home or organization may have systems or devices that are not connected to the internet or are not accessible from outside your local network.
Such non-internet facing systems can include internal servers, closed-circuit television (CCTV) systems, or standalone security systems that operate independently within your premises.
In these situations, the risk of external intrusion or hacking is significantly lower compared to systems that are directly exposed to the internet. Since the systems are not accessible to external threats, the implementation of an IDS may not be necessary.
However, it’s important to note that while these systems may not require an IDS, they should still have appropriate security measures in place to protect against physical breaches and internal threats. This can involve implementing access control measures, conducting background checks for employees with access to the systems, and regularly monitoring and auditing the internal network.
If you have a mixed environment with a combination of internet-facing and non-internet facing systems, it is important to differentiate between the two and apply appropriate security measures accordingly.
While non-internet facing systems may not require an IDS, it is important to regularly assess the security landscape and adapt to changing threats. New vulnerabilities and attack vectors can emerge over time, even for systems that are not directly connected to the internet. Therefore, staying vigilant and implementing appropriate security measures is still crucial.
Ultimately, the decision to implement an IDS for non-internet facing systems should be based on a comprehensive evaluation of the specific risks, access control measures, and the overall security objectives of your home or organization.
If you have a very small network with only a few devices and limited internet activity, you may not need an intrusion detection system. It’s important to assess the size and complexity of your network before investing in an IDS.
Legal and Regulatory Constraints
When considering the implementation of an Intrusion Detection System (IDS), it is important to take into account any legal and regulatory constraints that may exist. Depending on your jurisdiction, there may be laws or privacy regulations that restrict the use of certain surveillance or monitoring systems.
For example, some countries have strict regulations governing the collection, storage, and use of personal data. These laws aim to protect individual privacy and ensure that any data collected is used only for legitimate purposes. In such cases, deploying an IDS that captures and stores personally identifiable information (PII) may be in violation of the law.
Additionally, there may be specific regulations that dictate the circumstances under which certain surveillance technologies, such as cameras or audio recording devices, can be used. Failure to comply with these regulations can result in legal consequences and damage to your reputation.
Before implementing an IDS, it is crucial to research and understand the legal and regulatory landscape in your jurisdiction. This may involve consulting with legal experts or privacy consultants who can provide guidance on the applicable laws and ensure that your security measures align with the legal requirements.
If the use of an IDS is restricted by law or regulations in your region, you may need to explore alternative security measures or find ways to minimize the potential impact on individual privacy. This could involve anonymizing or encrypting data, implementing strict access controls, or obtaining explicit consent from individuals who may be captured by the surveillance system.
By complying with legal and regulatory constraints, you can ensure that your security measures are both effective and lawful, striking the right balance between protecting your property and respecting individual privacy rights.
Cost-Effectiveness Considerations
While an Intrusion Detection System (IDS) can provide valuable security benefits, it is important to assess the cost-effectiveness of implementing such a system. The costs associated with purchasing, installing, and maintaining an IDS can vary significantly depending on factors such as the size of your property and the complexity of your security needs.
Before investing in an IDS, it is crucial to evaluate whether the potential benefits outweigh the costs. Consider the following factors:
1. Risk assessment: Conduct a thorough analysis of the risks specific to your property or organization. Assess the likelihood and potential impact of security breaches to determine if an IDS is a justifiable expense.
2. Alternative security measures: Explore other security solutions that may offer a comparable level of protection at a lower cost. For example, implementing robust physical security measures, such as reinforced doors and windows, may be more cost-effective depending on your risk profile.
3. Ongoing operational costs: In addition to the upfront investment, consider the ongoing expenses associated with maintaining and managing the IDS. This can include licensing fees, software updates, and monitoring services. Evaluate whether these costs align with your budget and long-term security requirements.
4. Scalability: Consider whether the IDS can easily scale up or down as your security needs change. If you anticipate future growth or expansion, it is important to assess whether the system can adapt without incurring significant additional costs.
5. Return on investment (ROI): Determine if the expected benefits of implementing an IDS, such as prevention of loss or mitigation of risks, justify the financial investment. Calculate the potential ROI based on factors such as reduced insurance premiums, prevention of theft or damage, and increased peace of mind.
By carefully considering the cost-effectiveness of an IDS, you can make an informed decision that aligns with your financial resources and security priorities. Remember that security is a multi-layered approach, and while an IDS can be beneficial, it should be part of a comprehensive security strategy that takes into account your specific circumstances and budget.
Expertise and Knowledge Limitations
Implementing and maintaining an Intrusion Detection System (IDS) requires a certain level of expertise and knowledge. If you or your organization lacks the necessary technical skills or resources to properly configure and manage an IDS, it may not be the most effective security solution for you.
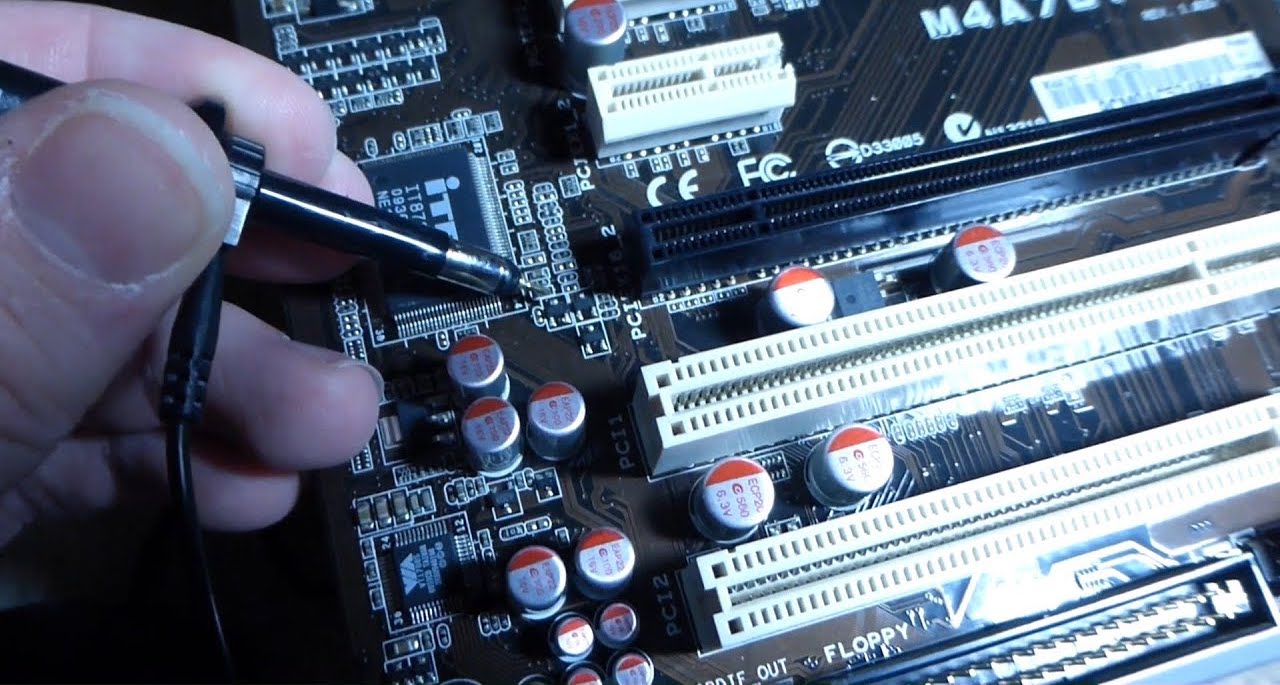
Setting up an IDS involves understanding network architecture, security protocols, and the various types of threats and vulnerabilities that can be encountered. Without the requisite expertise, attempting to deploy an IDS may result in misconfigurations or false positives, rendering the system ineffective and potentially creating more security vulnerabilities.
Additionally, IDS systems require regular monitoring and analysis of logs and alerts to identify potential security incidents. This requires a dedicated team with the knowledge and experience to interpret and respond to the data generated by the IDS.
If you do not possess the expertise or have the capacity to develop the necessary skills internally, it may be more practical to rely on external security providers who specialize in IDS implementation and management. Outsourcing the task to professionals not only ensures that the system is properly configured but also frees up your resources to focus on other critical aspects of your organization.
Furthermore, it is essential to stay up to date with the latest trends and developments in the field of intrusion detection. Cyber threats are continually evolving, and IDS systems need to be regularly updated to effectively detect and mitigate new attack vectors. This requires ongoing education and staying informed about the latest security practices and technologies.
By acknowledging your expertise and knowledge limitations, you can make an informed decision about whether an IDS is the right choice for your security needs. It may be more prudent to invest in other security measures that align with your capabilities and resources while still providing adequate protection for your home or organization.
Conclusion
Deciding whether or not to have an Intrusion Detection System (IDS) requires careful consideration of various factors specific to your situation. While an IDS can be a valuable tool in enhancing home security and surveillance, there are circumstances where it may not be necessary or the most practical solution.
Lack of sufficient resources, living in a low-risk environment, industry-specific exceptions, non-internet facing systems, legal and regulatory constraints, cost-effectiveness considerations, and expertise limitations are all important factors to evaluate when determining the need for an IDS.
Understanding your financial capabilities and the specific risks you face is crucial in making an informed decision. If resources are limited, alternative security measures may be more appropriate. Similarly, living in a low-risk environment may mean that other security measures can adequately address the minimal threats that exist.
Industry-specific regulations and legal constraints should also be carefully considered. Compliance with these requirements is essential to ensure that your security measures align with legal obligations and protect individual privacy rights.
Cost-effectiveness is another key consideration. Assessing the long-term expenses associated with implementing and maintaining an IDS can help you determine if the benefits justify the investment. It is also important to evaluate your organization’s expertise and knowledge limitations and determine if implementing and managing an IDS internally is feasible or if outsourcing to experts is a better option.
In conclusion, there is no one-size-fits-all answer to whether you should have an IDS. Each situation is unique, and it is crucial to assess your specific circumstances, risks, resources, and legal obligations when making a decision. By considering these factors carefully, you can implement a comprehensive security strategy that addresses your needs effectively and maintains the safety and protection of your home or organization.
Frequently Asked Questions about When Should I Not Have An Intrusion Detection System
Was this page helpful?
At Storables.com, we guarantee accurate and reliable information. Our content, validated by Expert Board Contributors, is crafted following stringent Editorial Policies. We're committed to providing you with well-researched, expert-backed insights for all your informational needs.